Criminal modification of identity theft of the manager of a company or a provider
Criminal modification of identity theft of the manager of a company or a provider.
Features:
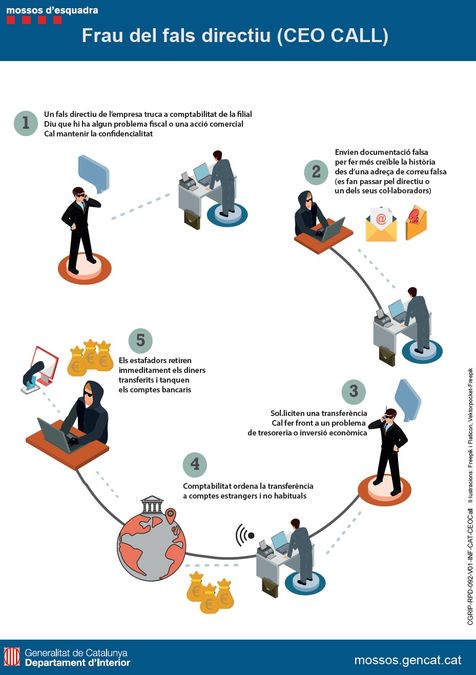
• The criminals supplant the identity of the President of a company, which is contacted by telephone or by email with those responsible for the administration or accounting services of a subsidiary. This false leader orders them to make transfers to bank accounts other than those of the company and that they are even in countries with a certain opacity or with particular fiscal characteristics.
• The false leader requests maximum confidentiality and will also provide, by means of a lawyer, false documentation so that the scammed people can give credibility to the requests they have made.
• When fraud is detected, it is already impossible to contact scammers or recover the money transferred from the accounts, since they have often ceased to be operational.
• The scam is committed in different modalities, depending on the phone calls made (CEO CALL, Chief Executive Officer - Call) or by email (MAILER).
• There have also been cases in which it is simulated to be a provider of the company.
Recommendations
By the company
• Make the security protocol diffuse where you specify which people can order economic transfers and what should be the procedure to carry them out.
• Disseminate the organization chart of the company with the objective that all the personnel know what are the people who configure the structure and how to contact (telephone and electronic mail).
• Establish an internal protocol for notifications of bank accounts by suppliers.
• In addition to requesting the bank certificate of the new account, always confirm with your provider by phone.
• For bank transfers of large amounts of money, adopt a "double verification" system with the banking entity to authorize them (e-mail-phone, for example).
• Establish a secure communication system by email - through digital signatures - with customers and suppliers.
• Be suspicious of money transfers to banks located in countries that have no relationship with the country of their provider.
• Many fraudsters use prepaid fraudulent orders or bills. It is for this reason that it is important to review the documents often and change the design or format, or apply verification measures.
On the part of the workers
• In the case of receiving a call from your boss in which you request the collaboration for a topic of maximum relevance, check the telephone number and compare it with that of the organization chart of the company.
• To inform another person in charge.
In case you have doubts that the person who sends you the e-mail message is really who it claims to be, call the number that you have recorded or that appears on the company's website, and not the one that appears in the same email they are directed to.